Verified Evidence
Every claim on this page is substantiated by macOS Activity Monitor. These screenshots were captured during an active transcription session.
Zero Network Traffic
Claim: Airgap Voice sends zero bytes over the network.
Evidence: macOS Activity Monitor confirms
0 bytes sent, 0 bytes received,
0 packets sent, and 0 packets received
while the application is actively transcribing.
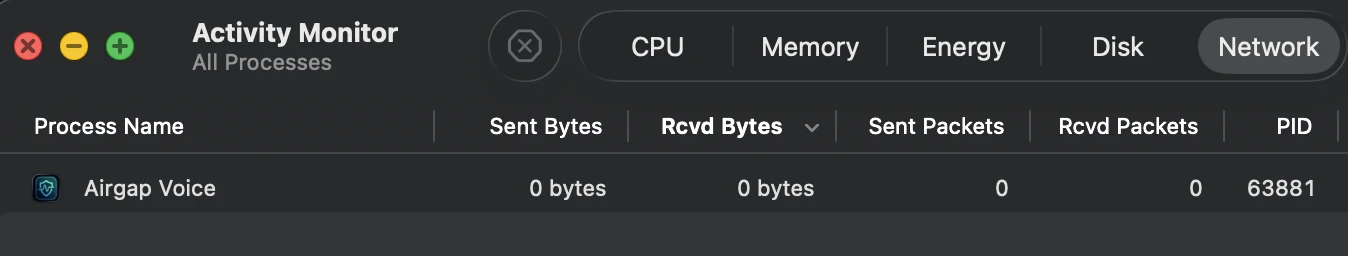
Activity Monitor → Network tab · Captured during active transcription session
Zero Disk Writes
Claim: No transcripts, audio, or session data are written to
disk.
Evidence: Activity Monitor shows
0 bytes written to disk. The 2.36 GB read is the one-time model load
into GPU memory at startup. After that, all processing stays in volatile RAM.
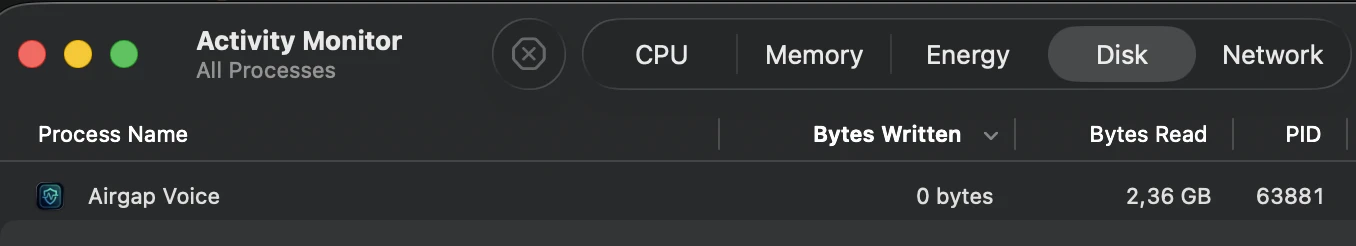
Activity Monitor → Disk tab · 0 bytes written confirms no forensic footprint
Local GPU Processing Confirmed
Claim: The AI model runs on your Mac's GPU, not a remote
server.
Evidence: Activity Monitor shows
38.4% GPU utilization and 1:24 GPU time during active
transcription.
The process runs 41 threads on Apple Silicon with the process kind listed as "Apple,"
confirming native Metal GPU acceleration.
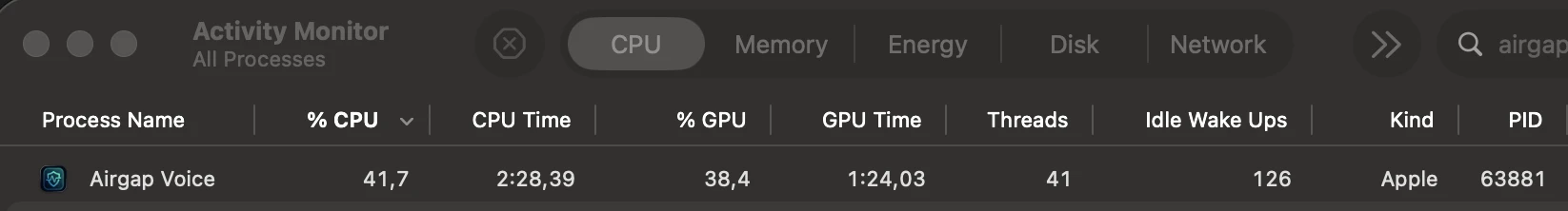
Activity Monitor → CPU tab (GPU columns enabled) · Native Apple Silicon Metal acceleration
Don't take our word for it. Open Activity Monitor on your own machine and verify these numbers yourself.